Demystifying MCP for Oracle GoldenGate Management
If you have been anywhere near the AI conversation lately, you have heard the term Model Context...
If your Oracle GoldenGate Extract process is running under a SQL Server user with the db_owner role, you are not alone. It is one of the most common shortcuts in the replication world, and it works without complaint. But working and being secure are two very different things. That shortcut is quietly introducing risk into your environment every single day it remains in place.
Oracle GoldenGate is widely regarded as the industry standard for real-time data replication. It powers mission-critical data pipelines across thousands of enterprises, moving transactional data between heterogeneous databases with speed and reliability. The challenge is not whether GoldenGate can do the job. The challenge is whether your team has configured it in a way that respects the security posture your organization demands.
When a database administrator assigns the db_owner fixed database role to the GoldenGate service account, the intent is usually simple: make it work, move on to the next task. The result, however, is anything but simple. The db_owner role grants unrestricted control over the entire database. That means the GoldenGate user can read every table, modify every row, alter every schema object, and even drop tables entirely.
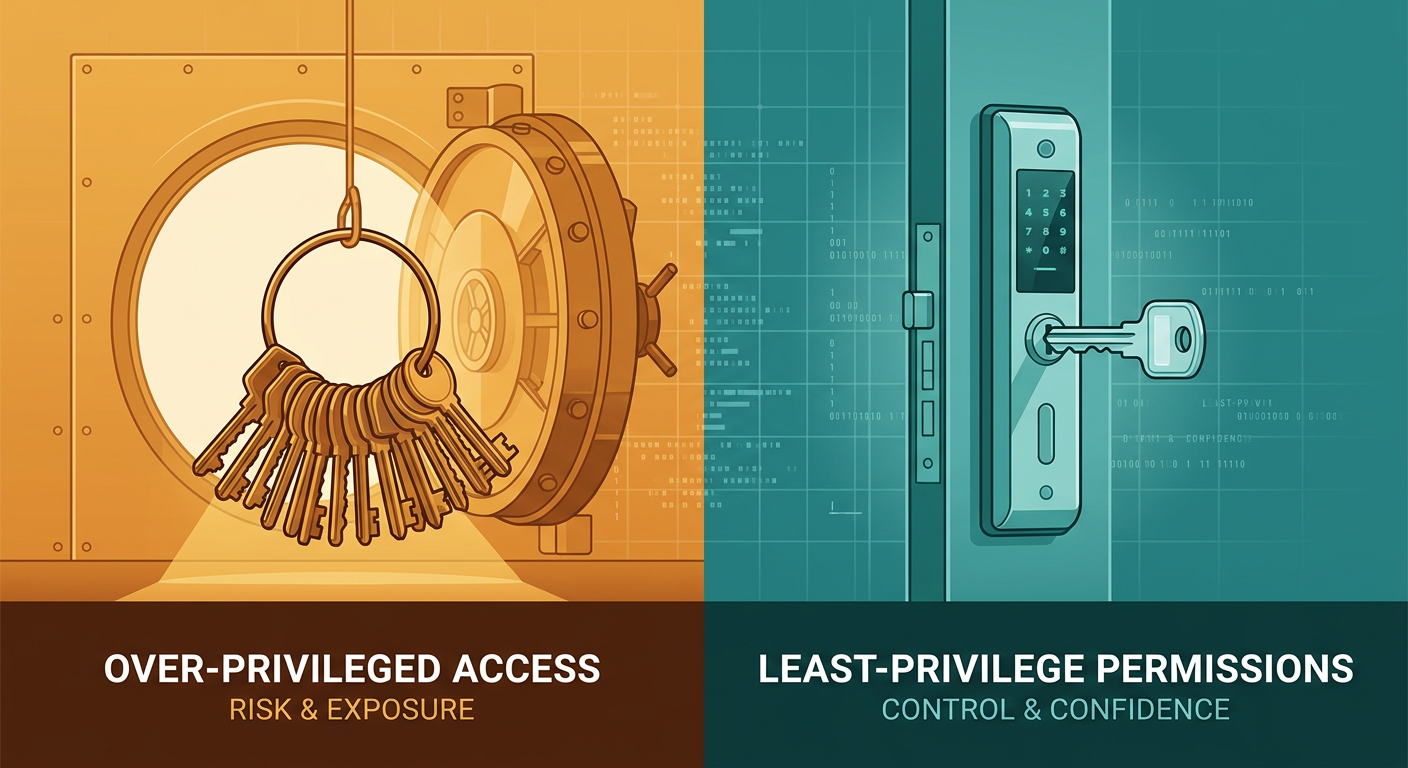
Think about that for a moment. The GoldenGate Extract process exists to do one thing: read committed transactions from the transaction log and pass them downstream. It does not need to insert data. It does not need to alter table structures. It certainly does not need the ability to delete objects. Yet with db_owner, it has the authority to do all of those things and more.
This creates two serious problems that every IT leader should be aware of.
First, the attack surface expands dramatically. If the GoldenGate service account credentials are ever compromised, an attacker inherits full control of the database. They can exfiltrate data, modify records, or cause destructive damage, all through a single account that was only supposed to be reading change data.
Second, it creates a compliance and audit headache. Regulatory frameworks like SOX, HIPAA, PCI-DSS, and GDPR all emphasize the principle of least privilege. When an auditor sees a service account with db_owner access and asks your team to demonstrate that the account has never been used beyond its intended scope, the burden of proof falls on you. Proving a negative is always difficult, and it becomes nearly impossible when the account technically has the authority to do anything.
The principle of least privilege is straightforward: every user, service account, and process should operate with the minimum set of permissions required to accomplish its task. Nothing more, nothing less. It is a foundational concept in information security, and it applies directly to how GoldenGate should be configured against SQL Server.
The good news is that Oracle GoldenGate supports a configuration model on SQL Server that aligns perfectly with this principle. It relies on Change Data Capture, a native SQL Server feature that captures row-level changes from the transaction log and stores them in dedicated system tables. By leveraging CDC, the GoldenGate Extract process can read changes without needing broad database privileges.
The setup involves two distinct phases, each with a clearly defined scope of responsibility.
Phase one is a one-time environment preparation performed by a database administrator who holds sysadmin privileges. This administrator enables CDC at the database level and then activates it on each table that GoldenGate needs to replicate. This step creates the CDC infrastructure, including the change tables and the capture jobs that populate them. Once complete, the sysadmin's involvement is finished. This is not an ongoing requirement, and the sysadmin account is not used by GoldenGate at runtime.
Phase two is the ongoing operational configuration. A dedicated GoldenGate service account is created and granted a narrow, specific set of permissions. These permissions allow the account to:
That is the entire permission footprint. The GoldenGate user cannot modify data in application tables. It cannot alter schemas. It cannot create or drop objects. It cannot grant permissions to other users. Its scope is tightly contained to the read-only operations that the Extract process actually requires.
Adopting the least-privilege model for GoldenGate is not just a technical best practice. It delivers tangible business value across several dimensions that matter to executives and IT leadership.
Reduced security exposure is the most immediate benefit. By confining the GoldenGate account to CDC read operations, you eliminate an entire class of risk. Even in a worst-case credential compromise scenario, the damage is limited to read access on change data, not full database control.
Streamlined audit and compliance cycles become possible when your permission model is clean. Instead of spending hours explaining to auditors why a service account has db_owner and building compensating controls around it, you can present a permission set that speaks for itself. The account can read change data. That is all. Auditors understand and appreciate that level of clarity.
Operational confidence improves across the team. When a service account is scoped correctly, there is no risk of an automation mistake or a misconfigured process accidentally modifying production data through the replication account. The permissions themselves act as a guardrail that protects the environment from unintended consequences.
Separation of duties is enforced naturally. The sysadmin who sets up CDC is not the same account that runs in production. The GoldenGate user that captures changes does not have the authority to modify the environment it monitors. This clean separation aligns with governance frameworks and reduces the risk of privilege escalation.
Teams sometimes resist this approach for a few reasons. The most common objection is that db_owner is faster to configure and easier to troubleshoot. While that is technically true, the time saved during initial setup is trivial compared to the cost of a security incident or a failed compliance audit. A few extra minutes of permission configuration is an investment that pays dividends for the life of the deployment.
Another objection is that the documentation or a legacy configuration guide recommended db_owner. Documentation evolves, and security expectations have changed dramatically in recent years. What was acceptable in 2015 may be a finding in a 2026 audit. Teams should treat permission models as living configurations that deserve periodic review.
If your GoldenGate environment is currently running with db_owner, the path to remediation is clear. Work with your DBA team to enable CDC on the target databases and tables, create a dedicated service account with the scoped permission set, validate that Extract continues to function correctly, and then revoke the db_owner role from the old account.
This is not a disruptive change. It can be performed during a standard maintenance window with minimal risk to the replication pipeline. The Extract process does not care whether its permissions come from db_owner or from a carefully scoped grant. It only cares that it can read the data it needs.
Oracle GoldenGate remains one of the most powerful tools available for real-time data replication. But power without discipline creates risk. By moving away from the db_owner shortcut and adopting a least-privilege permission model built on Change Data Capture, your organization gains the security, compliance readiness, and operational confidence that modern data environments demand.
The question is not whether your GoldenGate Extract will work with db_owner. It will. The question is whether your organization can afford the risk of leaving it that way.
If you have been anywhere near the AI conversation lately, you have heard the term Model Context...
Your senior DBA just spent 20 minutes trying to remember which port number connects to the...
You know what I learned after presenting the same session six times in eight days? People don't...